Attacks that target the web browser’s human element—the user—by using social engineering can be very effective. The developers of web browsers are placing greater emphasis on this attack vector. They do this by providing better guidance to the user regarding the risky actions taken by the website.
NSS Labs tested browsers’ ability to protect users from socially-engineered malware. According to NSS Labs, Internet Explorer surpassed the effectiveness of other browsers to protect the user from this attack vector.
Internet Explorer achieved such performance as the result of its improved SmartScreen feature, which incorporates application reputation capabilities starting with Internet Explorer 9. This aspect of SmartScreen maintains reputation data about known bad and known good executables. It also warns the user when the executable that he or she is attempting to run doesn’t have reputation data:

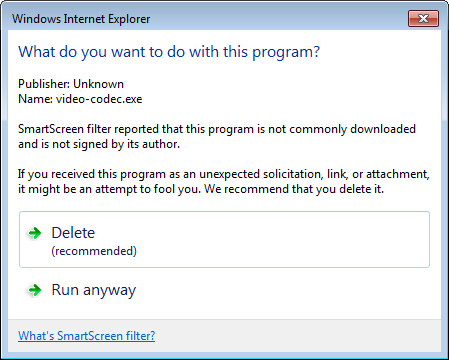
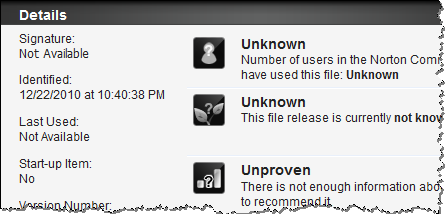
Anti-virus tools are starting to include similar capabilities, as you can see in the Norton Internet Security 2011 screen shot below; however, Internet Explorer’s improved SmartScreen feature is the first time I’ve encountered application reputation tracking built directly into the web browser.
Application reputation capabilities of end-point security tools help mitigate some risks associated with the user of the web browser executing a malicious program. Security awareness training is an important aspect of the mitigation strategy as well. So is limiting the privileges that the user has locally and on the network.
This note is part of a series that explores attacks that use the web browser. Other posts in this series are:
- Three Web Attack Vectors Using the Browser
- Mitigating Attacks on Web Applications Through the Browser
- Mitigating Attacks on the Web Browser and Add-Ons