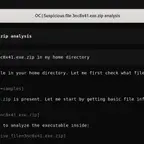
Practitioners who analyze malware for a living share insights on which approaches work well, how tools and methodologies are evolving, and what career paths exist for analysts. Topics include the role of automated sandboxes, go-to tools for code-level analysis, and techniques for examining non-standard specimens.
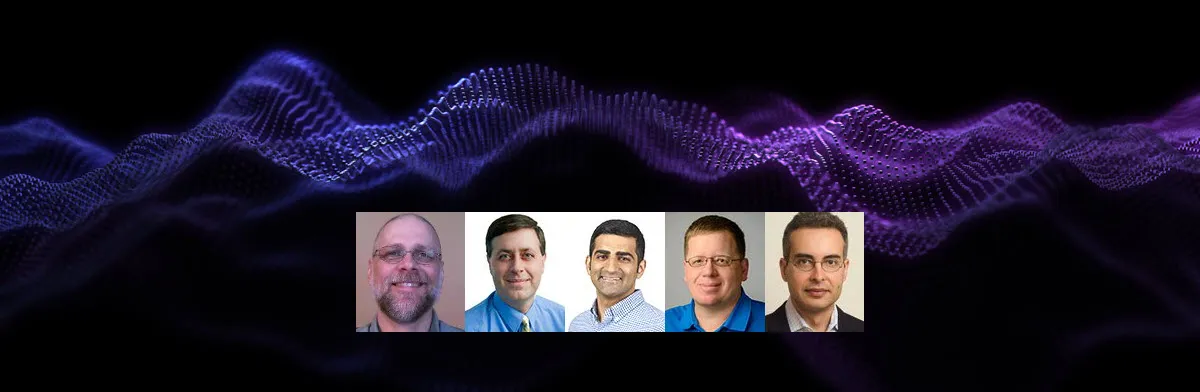
What malware analysis approaches work well? Which don’t? How are the tools and methodologies evolving? The following discussion—captured as an MP3 audio file—offers friendly advice from 5 malware analysts. These are some of the practitioners who’ve taught the reverse-engineering malware course (FOR610) at SANS Institute:
- Jim Clausing (Panelist)
- Evan Dygert (Panelist)
- Anuj Soni (Panelist)
- Jake Williams (Panelist)
- Lenny Zeltser (Moderator)
We covered the following questions. Here’s where you can find each of them in the recording, in case you’d like to jump to a specific topic:
- Which malware family or sample do you consider representative of or pivotal to a particular time period? (1:05)
- How has your approach to examining malware changed over the years? (7:17)
- What role do automated sandboxes play in the analysis process? (14:30)
- What are your go-to tools for code-level analysis? (20:15)
- Which malware analysis tools are useful for people who are just getting started with this type of work? (27:21)
- What advice do you have for analyzing malware that’s not a standard compiled Windows executable? (34:55)
- How often do you see malware that uses a technique you consider innovative? (39:01)
- Is endpoint security software becoming more effective at detecting malware? How are malware authors evading detection? (41:30)
- What aspects of malware analysis have become easier? What’s getting harder? (46:06)
- What are the career paths for individuals who analyze malware for a living? (53:52)
Many thanks to Jim, Evan, Anuj, and Jake for sharing their insights during this panel discussion, which I had the privilege of moderating. If you’d like to strengthen your malware analysis skills, take a look at the FOR610 course we teach at SANS Institute.