REMnux® offers a curated collection of free tools for reverse-engineering or otherwise analyzing malicious software. How to find the right tool for the job, given how many useful utilities come as part of the distro?
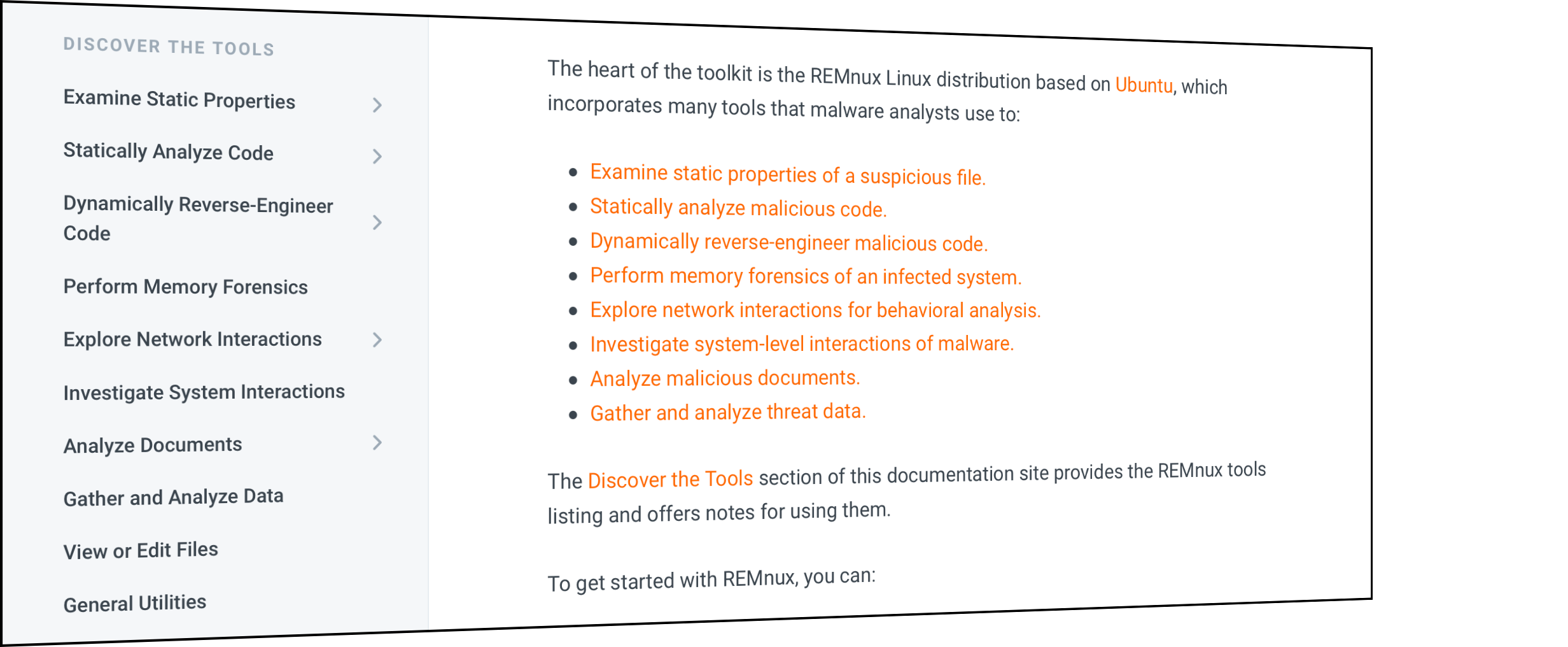
To guide you through the process of examining malware, REMnux documentation lists the installed tools by category. Each grouping, which you'll find in the Discover the Tools section of the documentation site, represents the type of actions the analysts might need to take:
- Examine static properties of a suspicious file: General, PE files, ELF files, deobfuscation
- Statically analyze malicious code: General, unpacking, PE files, Python, Java, Flash, Android
- Dynamically reverse-engineer malicious code: General, shellcode, scripts, ELF files
- Perform memory forensics of an infected system
- Explore network interactions for behavioral analysis: Monitoring, connecting, services
- Investigate system-level interactions of malware
- Analyze malicious documents: General, PDF, Microsoft Office, Email messages
- Gather and analyze threat data
In addition to providing numerous tools as part of the REMnux distro, the project also offers several malware analysis tools as Docker images. These will let you deobfuscate JavaScript and data, analyze websites, decompile executables, perform memory forensics, and more.
For another perspective on the REMnux tools you can use for examining malicious software, see the one-page REMnux Usage Tips cheat sheet.
To learn about the analysis workflow within which you can use these tools, take a look at my article Mastering 4 Stages of Malware Analysis.