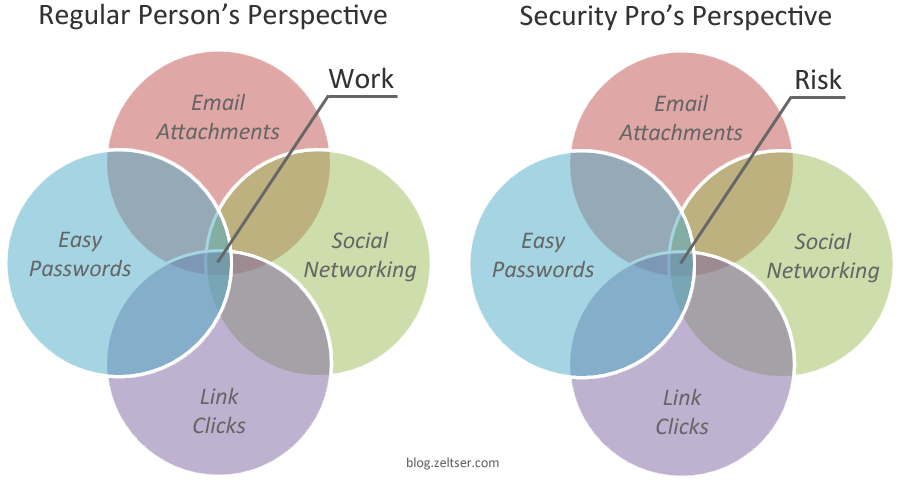
The gist of how regular people differ from security professionals in their perspectives on activities that affect information security:
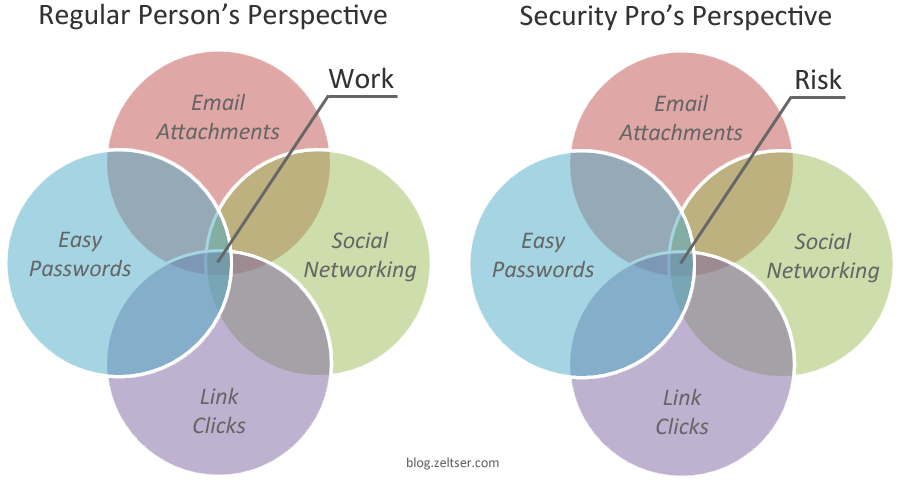
My conclusion: While there’s the need to control the actions that might put the organization’s data and compliance at risk, a security program should be designed with the assumption that people will find ways around security measures to get work done in a way that suits them best.
About the Author
Lenny Zeltser is a cybersecurity executive with deep technical roots, product management experience, and a business mindset. He has built security products and programs from early stage to enterprise scale. He is also a Faculty Fellow at SANS Institute and the creator of REMnux, a popular Linux toolkit for malware analysis. Lenny shares his perspectives on security leadership and technology at zeltser.com.