Scammers use a variety of social engineering tactics when persuading victims to follow the desired course of action. One example of this approach involves including in the fraudulent message personal details about the recipient to "prove" that the victim is in the miscreant's grip. In reality, the sender probably obtained the data from one of the many breaches that provide swindlers with an almost unlimited supply of personal information.
Personalized Porn Extortion Scam
Consider the case of an extortion scam in which the sender claims to have evidence of the victim's pornography-viewing habits. The scammer demands payment in exchange for suppressing the "compromising evidence." A variation of this technique was documented by Stu Sjouwerman at KnowBe4 in 2017. In a modern twist, the scammer includes personal details about the recipient—beyond merely the person's name—such as the password the victim used:
"****** is one of your password and now I will directly come to the point. You do not know anything about me but I know alot about you and you must be thinking why are you getting this e mail, correct?
I actually setup malware on porn video clips (adult porn) & guess what, you visited same adult website to experience fun (you get my drift). And when you got busy enjoying those videos, your web browser started out operating as a RDP (Remote Desktop Protocol) that has a backdoor which provided me with accessibility to your screen and your web camera controls."
The email includes demand for payment via cryptocurrency such Bitcoin to ensure that "Your naughty secret remains your secret." The sender calls this "privacy fees." Variations on this scheme are documented in the Blackmail Email Scam thread on Reddit.
The inclusion of the password that the victim used at some point in the past lends credibility to the sender's claim that the scammer knows a lot about the recipient. In reality, the miscreant likely obtained the password from one of many data dumps that include email addresses, passwords, and other personal information stolen from breached websites.
Data Breach Lawsuit Scam
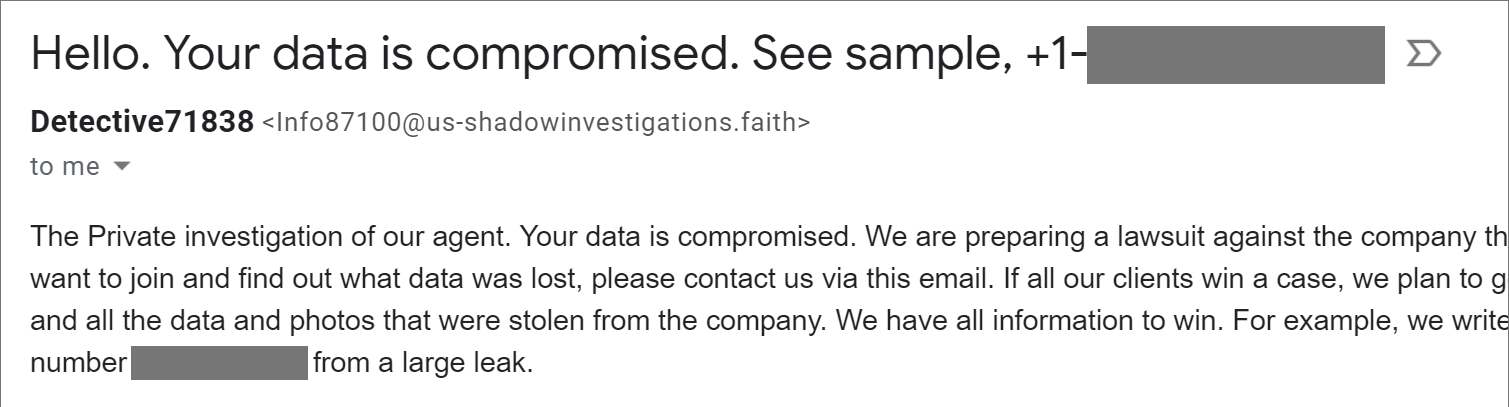
In another scenario, the scammer uses the knowledge of the victim's phone number to "prove" possession of sensitive data. The sender poses as an entity that's preparing to sue the company that allegedly leaked the data:
"Your data is compromised. We are preparing a lawsuit against the company that allowed a big data leak. If you want to join and find out what data was lost, please contact us via this email. If all our clients win a case, we plan to get a large amount of compensation and all the data and photos that were stolen from the company. We have all information to win. For example, we write to your email and include part your number ****** from a large leak."
The miscreant's likely objective is to solicit additional personal information from the victim under the guise of preparing the lawsuit, possibly requesting the social security number, banking account details, etc. The sender might have obtained the victim's name, email address and phone number from a breached data dump, and is phishing for other, more lucrative data.
What to Do?
If you receive a message that solicits payment or confidential data under the guise of knowing some of your personal information, be skeptical. This is probably a mass-mailed scam and your best approach is usually to ignore the message. In addition, keep an eye on the breaches that might have compromised your data using the free and trusted service Have I Been Pwned by Troy Hunt, change your passwords when this site tells you they've been breached, and don't reuse passwords across websites or apps.
Sometimes an extortion note is real and warrants a closer look and potentially law enforcement involvement. Only you know your situation and can decide on the best course of action. Fortunately, every example that I've had a chance to examine turned out to be social engineering trick that recipients were best to ignore.
To better under understand persuasion tactics employed by online scammers, take a look at my earlier articles on this topic:
- When Targeted Attacks Aren’t Targeted: The Magic of Cold Reading
- How the Scarcity Principle is Used in Online Scams and Attacks
- A Close Look at PayPal Overpayment Scams That Target Craigslist Sellers