Passwords suck. We cannot remember them. We dread having to type them. We struggle with safeguarding them. Yet, passwords are so ubiquitous, it's hard to get rid of them. Judging by the frequency with which we to continue to rely on passwords, the reports of their demise have been greatly exaggerated. However, the manner in which we use passwords is rapidly changing for the better, improving upon both convenience and security.
It's Practical to Type Passwords Less Often
An increasing number of applications and devices allow people to authenticate using means other than passwords much of the time, requesting passwords only when absolutely necessary.
Manufacturers have been including fingerprint readers in laptops for a while. After logging into the system by simply swiping a finger for a few weeks, it's easy to forget one's password altogether. Windows 10 will also support face and iris-based authentication. However, the password is still needed for situations when the fingerprint fails to work. This is an indicator of the passwords' likely role in the future.
Apple popularized fingerprint authentication for phones via its Touch ID fingerprint reader. Other mobile device vendors are either in the process of bringing similar technology to their products or have already done so. (Apple's purchase of AuthenTec made it unavailable to competitors and set them back by a few years.) Though users need to enter a traditional PIN once in a while, the authentication experience is less seamless.
Device and application providers seem to look for ways to avoid unnecessarily prompting users to authenticate themselves, decreasing the number of times passwords need to be entered. For instance:
- Google might normally keep a user's session active for a month, but prompt for a password earlier if it detects a security anomaly. The fewer times the person needs to type their password, the less frustrating their experience of using the service.
- Apple Watch minimizes the need for its wearers to authenticate themselves prior to using Apple Pay: The watch requests that the person authenticate to the iPhone when putting on the watch. Afterwards, the watch won't ask for authentication unless it senses that the person took off the watch.
It's Easier to Use Complex Passwords
Allowing people to enter their passwords less frequently lowers the "penalty" that users used to incur when selecting difficult-to-type passwords that were hard to guess. If authenticating to your laptop or phone using a fingerprint, it's easier to justify selecting a complex password, since you won't have to type it very often.
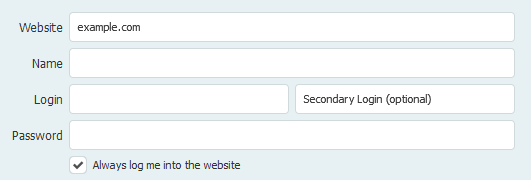
Since complex passwords are hard to remember, the need for password vaults has never been greater. Such applications allow users to generate unique and complex passwords, freeing people from the burden of having to remember them. The person only needs to memorize a single master password, and in some cases can even open the vault using a fingerprint. Password vault applications, such as 1Password, Dashlane (screenshot below) and LastPass have been improving their user interfaces, increasing the appeal of these once-niche tools to the general population.
People are more likely to use complex passwords if they have fewer passwords to remember. That's why it's also encouraging to see applications that employ delegated authentication, which gives people the opportunity to use existing logon credentials with providers such as Google and Facebook for logging into other websites. For instance, TripIt users don't have to create dedicated accounts for the service if they don't want to, as captured in the following screenshot.

In some cases, applications can automatically generate and provide users with one-time passwords that are difficult to guess. Google allows people to use complex application-specific passwords, which don't need to be memorized. Yahoo supports this, too. For another example, take a look at the on-demand passwords feature of Yahoo. It allows people to receive auto-generated one-time passwords when logging into the service, freeing them from having to memorize a traditional password.
In these scenarios, we're starting to see a distinction between the passwords people have to memorize for interactive logins and passwords that are used as transactional tokens and don't have to be remembered at all.
Using Weak Passwords is Less Risky
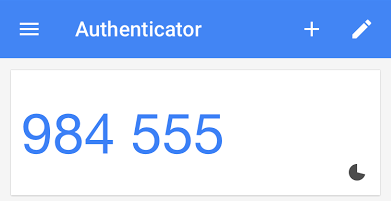
While the developments above encourage the use of hard-to-guess passwords, some factors make it less risky for people to select weak passwords. This is most applicable to websites that support two-factor authentication, provided with the help of SMS messages, hardware tokens and software apps such Google Authenticator (screenshot below). In these cases, it doesn't matter if users select passwords that are easy-to-guess, since the adversaries still need a way of intercepting or replicating the second authentication token.
In addition, application and service providers are starting to monitor for incidents where passwords may have gotten leaked, relying on threat intelligence feeds or monitoring sites such as Pastebin. People should not treat such measures as an encouragement to select bad passwords, but it's comforting to know about the safety net provided by a vendor that engages in such practices.
Passwords Won't Disappear Entirely
Although there are many options for innovative authentication mechanisms that go beyond passwords, it's hard to envision a future where passwords disappear entirely. For instance, passwords will be useful as a fail-safe mechanism when other authentication measures fail. There will also be scenarios where alternative authentication approaches are impractical or undesirable.
Fortunately, application developers are looking for ways to make passwords less annoying and risky. It's becoming easier to utilize complex passwords. We're starting to distinguish the passwords people type regularly and those they use as transactional authentication tokens. The need to type passwords is diminishing. In some cases, it has become less risky to use simple passwords.
The reports of passwords' demise have been greatly exaggerated, but we're minimizing their role in the Internet ecosystem, one use-case at a time.