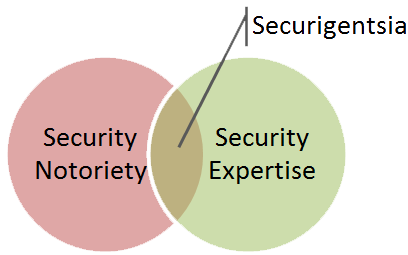
The information security community is comprised of many information security experts. Some of them enjoy public recognition of their expertise and form an informal group I call securigentsia. These individuals participate in meaningful public discourse and are generally perceived as improving the state and understanding of information security practices.
As I continue to engage in writing and public speaking activities myself, I wonder: To what extent is being recognized for one's expertise necessary for professional success? Is the quest for notoriety fueled merely by one's vanity, or is this tactic essential to making a difference in the security industry?
If a Tree Falls in the Forest…
We want to be heard. Perhaps that's why the number of bloggers has gradually increased among adults over the age of 33 according to a study by PewResearchCenter. (The number of younger bloggers subsided as they switched to social networking for on-line interactions.)
If an expert makes a discovery that can drastically improve the state and understanding of infosec practices, can he or she make a difference if no one hears about it? Writing on-line—assuming that the text is read by someone—is one way to gain public recognition of the person's expertise. Growing one's readership increases the likelihood of being heard.
Marketing One's Expertise On-Line
Having a respectable on-line persona has become essential for building one’s professional reputation. After all, it’s common practice to Google the person to find out who he or she is. In addition, building an on-line profile that describes one’s projects and achievements is critical for those who understand the decreasing importance of resumes during a job search.
Boasting one's expertise is in conflict with the character of many information security professionals. Yet, there appears to be value in assigning oneself a label such as "guru": Dan Zarrella’s research of on-line social networking practices showed that "Twitter accounts that use the word 'guru' tend to have 100 more followers than the average Twitter account."
Even those who don't feel right calling themselves "gurus" usually find it acceptable to create a professional bio that describes their accomplishments in a third voice and using a factual tone. The practice of including such bios in one's profile has become commonplace.
Another way of marketing oneself on-line without actively boasting one's accomplishments is writing articles and releasing projects that people find useful, thus allowing one’s work to "speak" on behalf of its author. If you have expertise in a particular area of information security, you can contribute to the community’s knowledge base by sharing your insights.
Getting Side-Tracked by Notoriety
In a paper about the role of deliberate practice in the acquisition of expert performance, the authors quote an earlier study of visual artists. According to the study, most of its subjects were drawn to painting because it allowed social isolation. However,
"Aspiring painters have to promote social relations with art dealers, art critics, and buyers to gain notoriety, increase the demand for their art, and generate sufficient sales for full-time artistic activity. Failure to do so forced many of the best artists to take another job unrelated to painting."
Similarly, information security experts striving for notoriety might get side-tracked. Gaining and maintaining the public’s attention takes effort that might divert the person’s attention from the domains where he or she achieved expertise.
It’s strange to be writing about this topic when I am putting effort into researching and documenting security topics that, I hope, strengthen my own information security "brand." Sorry for the somewhat disjointed thoughts on this matter, as I am still trying to make sense of the irresistible lure of notoriety.