Open-source sandbox platforms, analysis environments, and AI-assisted tools let you build your own malware analysis capability without commercial licenses. Options include CAPEv2, DRAKVUF Sandbox, REMnux, FLARE VM, and tools that connect AI agents to analysis environments.
Automating parts of malware analysis lets analysts focus on tasks that require human judgment. Researchers can choose from open-source sandboxes, pre-built analysis environments, and AI agents to augment and expand our capabilities. The tools below are free and locally installable. For web-based sandbox services, see my list of automated malware analysis services.
Automated Sandbox Platforms
Sandbox platforms execute malware in a controlled environment and record its behavior. They automate the observation step, producing reports on file, registry, network, and process activity:
CAPEv2 is the most widely used open-source malware sandbox. A fork of Cuckoo Sandbox, it extracts configurations and payloads from hundreds of malware families. It runs on Ubuntu with KVM virtualization. Active development and a large community-maintained rule set make it the standard starting point for a local sandbox.
DRAKVUF Sandbox takes an agentless approach to monitoring. Built by CERT Polska, it uses the Xen hypervisor to observe malware from below the guest OS. Because no monitoring component runs inside the guest, malware cannot detect or interfere with the analysis. The tradeoff: it requires Xen-compatible hardware and more setup than KVM-based alternatives.
Cuckoo3 is a Python 3 rewrite of Cuckoo Sandbox by CERT-EE. It modernizes the codebase and adds new analysis capabilities. It is under active development but has not yet reached CAPEv2’s breadth of malware family coverage or extraction rules. Keep an eye on it as the project matures.
Analysis Environments
Pre-built environments bundle hundreds of tools into a ready-to-use system. They save you the work of finding, installing, and configuring each tool individually:
REMnux is a Linux distribution I maintain for analyzing malicious software. It includes 200+ tools for examining executables, documents, scripts, and network artifacts. You can run it as a VM or use individual Docker containers for specific tools like Radare2, RetDec, and Thug. The latest REMnux also supports AI-assisted analysis, covered below. See the full tool catalog for what’s included.
FLARE VM is Mandiant’s Windows-based analysis distribution. It installs over 100 tools onto a Windows VM through a package manager. If you analyze Windows malware and need native debuggers and disassemblers, this toolkit will save you setup time.
AI-Assisted Analysis Tools
AI agents can plan analysis approaches, run tools, and interpret output. Several open-source projects can assist malware researchers in this way:
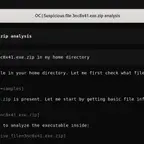
I built the REMnux MCP Server to connect AI agents to all REMnux tools. It encodes practitioner workflows: which tools to run for each file type, how to invoke them, and how to read the results. A single call can run a multi-tool pipeline against a sample. See my article on using AI agents to analyze malware on REMnux for walkthroughs and replays.
GhidraMCP and GhidrAssistMCP let AI agents drive Ghidra for reverse engineering. They can navigate functions, read decompiled code, and rename variables. (GhidrAssistMCP comes pre-configured on REMnux.)
r2ai is an AI plugin for radare2. It lets you query a language model about the binary you are analyzing from the radare2 command line.
Where to Go Next
If you are starting out, see How You Can Start Learning Malware Analysis and 5 Steps to Building a Malware Analysis Toolkit. To see how these tools fit the analysis process, read Mastering 4 Stages of Malware Analysis. For hosted sandbox services with no local setup, see Automated Malware Analysis Services.