
My earlier posts looked at examples of malvertising campaigns and explored how malicious ads function. In this note I look at the efforts that scammers put into protecting their ad-based attack campaigns.
Attackers do their best to make it harder for the advertisement networks to distinguish between benign and malicious ads. Obfuscating the logic implemented as part of the ad’s code—both HTML/JavaScript and Flash/ActionScript—is one way to do this. For instance, here’s an excerpt from a malicious web page using obfuscated JavaScript to evade detection and complicate analysis:
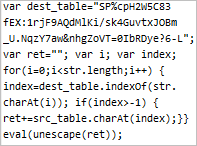
The script executes in the victim’s browser, recreating the original script on the file and executing it to implement the client-side attack.
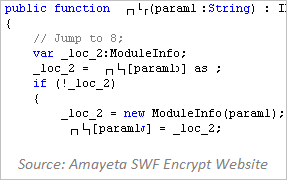
ActionScript included in malicious Flash ads can be obfuscated as well using a variety of techniques. One of these methods is implemented using a commercial (and non-malicious in itself) tool SWF Encrypt, rendering the code within a Flash program virtually unreadable.
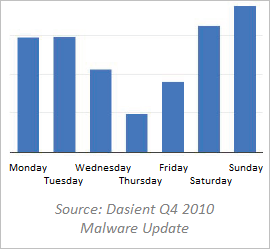
Another approach to protecting a malvertising campaign is to time it to take place over the weekend. The ad is often scheduled to begin displaying on Friday evening, but the malicious logic isn’t activated until early Saturday morning. This timing is designed to make it less likely that the advertisement network’s employees will be able to detect and quickly react to the malicious nature of the ad, since the staff probably isn’t at work during the weekend.
Unfortunately, it often takes a long time for the malicious ad to be disabled. Dasient’s Q4 2010 Malware Update reported the average lifetime of a malvertising campaign being about 10 days. Interestingly, according to Dasient’s data, Thursday appears to be the least popular day for malicious ads.
Attackers protect malvertising campaigns by carefully timing when the advertisements begin exhibiting malicious characteristics and also by obfuscating the code that implements the ad’s logic. These actions make it difficult for ad networks and end-users’ tools to distinguish between legitimate and malicious advertisements.
This note is part of a series of malvertising-related posts. You can also learn:
- Examples of Malicious Ad Campaigns
- The Mechanics of Malicious Ads
- How Malicious Ads Are Deployed
- Dealing With Malicious Ads - Who and How?