
My earlier posts looked at examples of malvertising campaigns, explored how malicious ads function and how they are protected. This note examines how scammers deploy malvertisements into the world, making them appear on numerous desktops, laptops and mobile devices across the web.
Sometimes, attackers compromise the ad network’s IT infrastructure to distribute malvertisements. This allows the attacker to directly control what banner ads are displayed, offering the ability of serving malvertisements or modifying legitimate ads to include malicious code or destinations. This seems to have been the case in the Unanimis incident that affected websites such as the London Stock Exchange. According to SC Magazine, Unanimis confirmed that the malvertisements were the result of unauthorized access to their systems.
Another, perhaps more common approach to injecting malvertisements into the web ecosystem involves impersonating agencies that supposedly represent legitimate clients wishing to advertise. This approach involves attackers spending money to pay for the malicious ad campaign. (But it takes money to make money, right? In any case, they are probably paying with stolen funds.)
For example, a scammer contacted Gawker Media pretending to be a popular ad agency:
"I work with Automotive and Entertainment clients in Spark. First and foremost, we want to run a performance campaign for Suzuki across your network. Our budget to start is $25k+."
In their phone and email interactions the scammer sounded professional and knowledgeable and was able to fool Gawker’s ad sales representatives into placing the accepting and displaying the ads that turned out to be malicious.

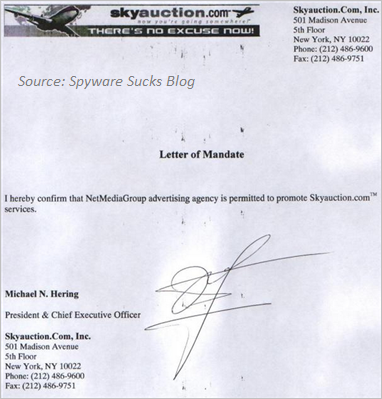
Sometimes attackers pretend to be associated with legitimate and well-known ad agencies. In other cases, attackers represent fake ad agencies pretending to represent legitimate clients who wish to launch an advertising campaign. They might even present the ad network with a falsified Letter of Mandate, claiming that the company being advertised authorized the ad agency to act on its behalf. For instance, SkyAuction.com reported the following incident according to the Spyware Sucks blog:
"We were contacted by another company today that were duped into hosting one of the fraudulent ads for a couple of days (which have since been taken down). It seems that the source of the ads is a company called NetMediaGroup (http://www.netmediagroup.net). They are claiming to represent us and even provided a fake letter of mandate.”
Attackers can deploy malicious advertisements by compromising the ad networks systems or by purchasing campaigns that distribute the malicious ads. These tactics allow attackers to run malicious code in browsers and applications of numerous users across the web, providing an effective initial attack vector.
This note is part of a series of malvertising-related posts. You can also learn:
- Examples of Malicious Ad Campaigns
- The Mechanics of Malicious Ads
- How Malicious Ad Campaigns Are Protected
- Dealing With Malicious Ads - Who and How?