Although malicious activities that involve LinkedIn aren’t as popular as those associated with other social networking sites, the service has seen its share of scams and fraud. The majority such incidents occurred outside of the LinkedIn website, and took the form of LinkedIn look-alike email spam. However, there have been cases where the scammers used the linkedin.com website itself to achieve their goals. Let’s take a look at some of them.
Using linkedin.com as a Redirector to Malicious Sites
It’s simple to use linkedin.com as a redirector to other websites at the moment. The URL needs to look like this to redirect you to Google, for instance:
Attackers benefit from “bouncing” users off a website that has a strong reputation, because doing so lends credibility to the link that ultimately will lead to a malicious site. Gerald Dillera at TrendLabs described one such attack that used linkedin.com. The incident involved Facebook wall posts that promised to show “The Video That Just Ended Justin Biebers Career For Good!”

When the potential victim clicked the link, Facebook showed a confirmation that the person is about to leave Facebook.com and be taken to linkedin.com. However, linkedin.com would redirect the person once more to a malicious domain. According to Gerald, “the cybercriminals behind this attack benefit from those who paid to answer the online survey. In addition, this can also pave the way for malware infection and information theft.”
Fraudulent Job Postings on LinkedIn
The LinkedIn Jobs site is designed to pair up job seekers with employers. Perhaps it’s not surprising that this service can act as a venue for distributing fraudulent job postings. The examples I’ve seen involved recruiting money mules, though the creators of these job postings did their best to make them look legitimate.
Consider one such posting, which has been live on LinkedIn for about a month as of this writing and carried the title “*** COME AND WORK WITH US ***”. This work-from-home job promised to pay a weekly salary and a 10% commission for “assisting us in processing the payments from our clients.” The responsibilities were described as follows:
"1. Recieve payment from Customers
2. Cash it at any cashing point or at your banks and you will deduct 10% which will be your percentage/payon Payment processed
3. Forward balance after deduction of percentage/pay to any of the offices you will be contacted to send payment to.(Payment is to forwarded either by Money Gram or Western Union Money Transfer.”
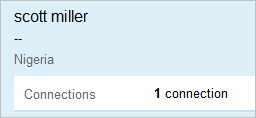
The posting claimed to be recruiting for a legitimate UK company. It was posted by “scott miller” with a mostly empty profile, 1 connection and the location of Nigeria.
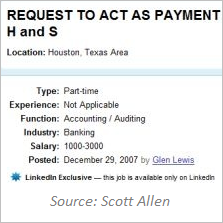
The text in the above job posting was very similar to the one that Scott Allen from LinkedIn Intelligence described in 2007. It was titled “REQUEST TO ACT AS PAYMENT REPRESENTATIVE” for H & S International Limited:
Criminals recruit money mules in an effort to get money earned through illegitimate means out of the country. In some cases, dedicated sites are set up for the recruiting effort. In others, traditional job sites, including LinkedIn, help with the hiring process.
Scams Sent to the LinkedIn Inbox
Like many other social networking sites, LinkedIn allows the site’s users to contact each other using an email-like messaging service. This functionality can be used to contact LinkedIn users for fraudulent purposes. LinkedIn users tend to be in a sociable frame of mind when visiting linkedin.com and checking the contents of the site’s Inbox; this might make them more vulnerable to scams.
For instance, some LinkedIn users received in their Inbox a message from Natasha Kone, whose text followed the narrative of a classic 419 scam:
"Before the death of my father on the 12th December 2007,in a private hospital here in Abidjan,he called me secretly to his bed side and told me that he kept a sum of $6.500 000… I am inclined to offer you 15% of the total sum as a way of compensation for your effort after the successful transfer of these fund to your nominated account overseas."
In such advanced fee scams, the target is persuaded to “advance sums of money in the hope of realizing a significantly larger gain” according to Wikipedia. Contacting potential victims using LinkedIn offers the scammer the potential to build a believable social networking profile that could put the target at ease.
Consider another scenario, which demonstrates, at best, questionable use of the LinkedIn website. Joseph Dowdy from MeshMarketer described receiving “an invitation through LinkedIn to become listed in Stanford Who’s Who.” Joseph wrote that because “the invitation was coming from LinkedIn, I thought it must be legit without having to do the footwork to see if it was a scam.”
Joseph later became suspicious of the service after noticing that the sample profile shown on Stanford Who’s Who’s website was using a photo of his friend without her approval. He noticed numerous complaints recorded about the company on the Rip-off Report website, alleging that it deceives people into paying large fees.
Wrapping it Up
As you can see, scammers have been using the LinkedIn website in several ways, including treating linkedin.com as a redirector to malicious sites, posting fraudulent ads and interacting with potential victims using the LinkedIn website. It’s interesting to note that while the platform provides numerous other opportunities for fraud, I haven’t seen many publicly-documented incidents of this nature.
This post is part of a series that explores LinkedIn scams, fraud and information security risks. The other posts are:
- Why There Are Fewer LinkedIn Scams and Malware Than Facebook Ones
- Exploring LinkedIn Look-Alike Email Spam Campaigns
- The Potential for Malicious Ads on linkedin.com
- The Use of Fake or Fraudulent LinkedIn Profiles