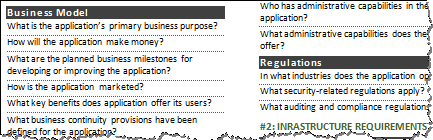
One of the cheat sheets I created offers tips for the design and review of a complex Internet application’s security architecture. It provides recommendations for considering the following security aspects of the application:
- Business requirements: You need to understand the purpose of the application, including what it does and how it makes money, to offer security recommendations.
- Infrastructure requirements: You need to understand network and operating system requirements of the application to create a comprehensive security design.
- Application requirements: You need to pay attention to application-level aspects of the security architecture, including access requirements and data flows.
- Security program requirements: You need to incorporate on-going procedural tasks into the security design to make sure the application’s security is maintained on on-going basis.
I created this security architecture cheat sheet (among others) because it’s easy to overlook a critical aspect of the application and its ecosystem when designing its security under time pressure. Specifically, I had the following three use-cases in mind for the Security Architecture cheat sheet:
- You can use it when examining an existing application as part of a security assessment
- You can use it when initially designing an application before starting to implement it
- You can use it as a reference for on-going maintenance of an existing application
Note that by “application” I mean a complex, multi-tier set of inter-dependent software and hardware components that process data and operate as part of the Internet’s ecosystem. In many cases, such applications are comprised of front-end web servers, application or middleware servers, databases, load balancers, firewalls, security monitoring systems and so on.
In addition to being available in an HTML format, the cheat sheet is also available as a printable two-page PDF file and as an editable Microsoft Word document.
Have you found the Security Architecture cheat sheet helpful? I’d love to hear how you use it and whether you have recommendations for improving it.