
Information security can fail in many ways, despite the best plans and intentions. That’s why we must design the security program with failure in mind. You should be able to detect suspicious activities before they escalate into major incidents. And when the data breach does occur, the security architecture should limit the incident’s scope, dampening the spread of malware or the attacker’s influence to give you time to respond.
We can learn how to account for the eventual failure of controls from the more established industries, such as boat-building. Consider the following excerpt from a stability certificate issued by the U.S. Coast Guard Marine Safety Center to a passenger boat:
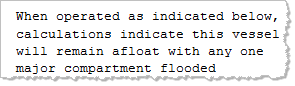
The boat was tested to stay afloat even when one of its compartments is flooded. (Click on the excerpt above to see the full text.) The authorities expect the vessel to be designed with failure in mind, recognizing that even when it is built and operated perfectly, an unexpected event may cause a hull breach.
Designing an information security architecture with failure in mind involves accounting for possible issues at network, system and application levels. For instance, accomplishing this at the network level might involve deploying multiple firewalls to segment the environment into several tiers according to risk.
In the words of Denis Waitley, “expect the best, plan for the worst, and prepare to be surprised.”
Hand-picked related items:
- 10 Information Security Mistakes: A False Sense of Security
- Firewall Deployment for Multitier Applications
- Common Failures of Information Security Tools