Pursuing vulnerabilities in local software that is accessible through the web browser has been an effective attack vector. The following 4 free tools can help you identify locally-installed browser plugins that are behind on security patches.
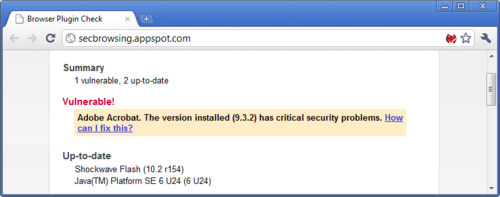
Google Chrome and Secbrowsing
Users of Google Chrome rejoice—the browser flags common insecure plugins without the need for any additional tools. The alert appears when you attempt to load content that makes use of the vulnerable plugin:
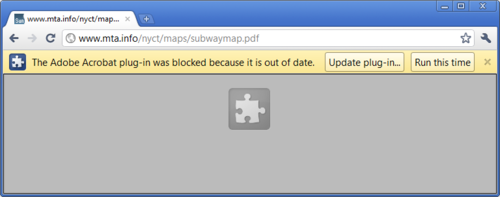
If you’d like to be notified of outdated plugins proactively, even before Google Chrome has the need to use the plugin, install the optional Secbrowsing extension from Google.
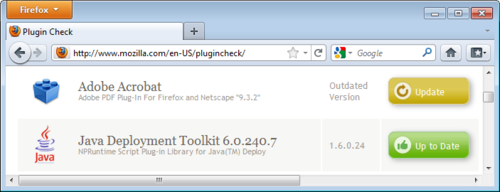
Mozilla Plugin Check Page
Mozilla set up the Plugin Check page identify insecure plugins. The page works in Firefox as well as other browsers, and doesn’t require any tool installation. Mozilla provided some technical details regarding inner-workings of the server-side tool for those seeking additional information about it.
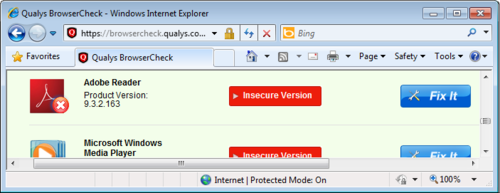
Qualys BrowserCheck
Qualys BrowserCheck is a free lightweight tool for scanning common browsers for vulnerable plugins. The tool needs to be installed locally, and is well documented by Qualys.
Secunia PSI
Secunia is well-known for Secunia PSI—a free local application to identify vulnerabilities in installed software. The tool is able to scan for not only insecure browser plugins, but also for vulnerabilities in other local software. The biggest issue with Secunia PSI is that the tool’s user interface is likely to be confusing for inexperienced computer users.

My Perspective
Secunia PSI rules when it comes to providing a comprehensive scan of local applications. In this, it exceeds the coverage of Qualys BrowserCheck, and would be my first choice if I were to install a scanner.
My kudos go to the Google Chrome team for building plugin-scanning capabilities directly into the browser. This approach has the potential of providing more complete and accurate results than the install-free Mozilla Plugin Check page, while providing the user with automatic alerting.